
The holidays are just around the corner and in the world of cybersecurity that means gift card scams will start hitting inboxes. [Read more…]

The holidays are just around the corner and in the world of cybersecurity that means gift card scams will start hitting inboxes. [Read more…]

Data breach investigations have revealed a new shift in the hacking landscape, criminals are going after your passwords with a vengeance. [Read more…]

You’re connected to cloud storage and file sharing, so you should be good to go having all your files backed up, right? Wrong! [Read more…]

Cloud applications have gone from being a productive way to provide anywhere access to becoming a business necessity in a world where remote workers are vital to keeping operations going when business-as-usual is interrupted.
Cloud services like Microsoft 365, G Suite, and others are now where many companies station their business workflows. This means their data is also more often stored in the cloud than in on-premises equipment.
Hackers have taken notice, and the latest Verizon Data Breach Investigations Report shows that they are going after those cloud application passwords with a vengeance.
Password dumpers have now become the #1 form of malware used in data breaches. In phishing attacks, login credentials have become the information most sought after.
How can you use the cloud effectively to keep your business data available to all your workers, no matter location, and ensure it is safe? We have several tips below for good cloud security.
Safe use of cloud solutions requires a strategic approach. You can’t just rely on the cloud provider to keep your data safe, especially when hackers are trying their hardest to steal legitimate user credentials that will give them an all-access pass to your account.
Here are some good cloud security practices to keep your business data protected.
Compromised passwords are responsible for 81% of hacking related data breaches.
Users often adopt bad password habits because of all the different passwords they have to use. These risky habits include:
It’s important to set up cloud platforms, such as Microsoft 365, to require the use of strong passwords and reject passwords that don’t meet certain criteria. This should include length requirements and the need to use at least one number and one symbol.
Adding a second factor to your logins using MFA can stop 99.9% of attempted account hacks, greatly increasing the security of your cloud accounts.
MFA simply involves having a secondary step added to login where the user is sent a time-sensitive code to a pre-approved device. That code then has to be entered to complete the login. This step keeps hackers out even if they’ve compromised the password.
Hackers may not make themselves immediately known, stealing data “under the radar” after they’ve managed to get into your cloud account. One way to detect this type of compromise is to monitor cloud account access.
Tools like cloud application security brokers and endpoint device managers can help you keep tabs on access patterns to your cloud solutions. This allows you to catch any suspicious activity, like large file downloads, when they happen.
Another way to monitor who is logging into your cloud accounts is to turn on account alerts. Many of the major cloud services will have these available in the security settings.
Account alerts can let you know things like:
Some businesses will leave old employee accounts open for a while after the employee has left. They want to make sure they don’t lose any data or may just get busy and keep putting off closing it until “later.”
Leaving old accounts open leaves your account at risk. Here are the steps you should take once an employee leaves to secure your account and data:
Many users stay logged into their cloud accounts because it’s easier than continually logging in and out. They also want to make sure they receive important account alerts.
But when a mobile device that’s logged into your company cloud accounts is lost or stolen, that means a stranger has a free pass to get in and do whatever they like.
Endpoint device protection allows you to manage all your endpoints remotely (mobile devices and computers). One of the important safeguards this provides your accounts, is that you can revoke access remotely at anytime from a device. Devices can also be locked and wiped remotely, reducing the risk that a thief will be able to access your company accounts and information.
With businesses so reliant on the cloud, it’s vital that you pay attention to cloud security. ProdigyTeks can help your Chicago business put the safeguards in place that you need.
Schedule a free phone consultation today! Call 312-600-8357 or reach us online.

One of the lasting impacts of the COVID-19 pandemic is going to be more remote workers. Most companies were forced into using remote teams during state lockdowns, and even post-pandemic, they plan to keep more workers telecommuting from home. [Read more…]

Cyberattacks and data breaches happen worldwide, and no one is immune. Your business needs to protect its networks and systems, and secure sensitive data. But how much do you know about the types of cybercriminal out there? This roundup discusses the biggest threats and what they’re after.
Cybercrime Gangs
Online crime is a lucrative industry. Cybergangs go online to offer “crime as a service.” Their targets vary and can be spread out globally. In 2019, one international crime gang stole $100 million from more than 40,000 victims. Culprits were found in the US, Bulgaria, Germany, Georgia, Moldova, and Ukraine. Victims included small businesses, law firms, international corporations, and nonprofits.
Many of these bad guys may have started out in the digital environment, but well-established street gangs are turning their attention to cybercrime too.
Typically well-funded and organized, cybergangs work long-term to mount large-scale attacks. They target banks, law firms, healthcare networks, and other big businesses.
Still, small businesses can be targeted by cybercrime gangs. You could be the first domino to compromise a larger, more lucrative target in your supply chain.
State-based Actors
One nation pays an individual or group to target another country. On the digital battlefield this could mean:
Australia recently announced a “sophisticated state-based cyberattack” on political and private-sector organizations.
State actors also used cyber techniques to damage Iran’s nuclear program. They left an infected thumb drive in the parking lot. A well-meaning staffer found the USB and plugged it into the facility computers. The virus caused Iran’s fast-spinning centrifuges to go into overdrive.
These attackers are often motivated by nationalism, but this doesn’t mean businesses are safe. A politically motivated cyber actor might target a hotel hosting an international convention or gain access to a government vendor to send false communications.
Lone Wolf
Also known as disorganized crime, this is the online equivalent of a petty thief. Many make their income stealing money from low-hanging targets.
Some Lone Wolves are only interested in proof-of-concept: hacking into businesses and governments to see if it’s possible, without doing any damage once they are inside.
Now that you better understand why your business might be targeted, it’s time to take the necessary steps. We can help solidify your cybersecurity stance. Partner with a managed service provider. Our experts can set up email security, remote access management, anti-malware scanning, and more. Contact us today at 312-600-8357!

Is there one thing we can count on now with COVID-19? The situation can change in an instant. You may have been confident in your business continuity plans in the past, but the pandemic has shaken us all up. It’s a solid reminder to review our plans to get back to business quickly and seamlessly.
A good business continuity plan ensures maintained operations before and during unexpected disruptions. Generally, decision-makers strategize in advance to ride out:
These could impact a system or network or prevent you from accessing your location to get to your computers and important data.
Now, we also know that we should prepare for the effects of an international health pandemic!
Such business-centric planning considers all necessary elements of staying on track. You’ll look at physical premises and staffing, and hardware and software requirements.
Preparing for the Unexpected
A business continuity plan tries to anticipate the worst that could happen. The problem is that we can never know what the next bad thing might be.
You may not ever need to use your plan, but taking a “these things happen to other businesses” point of view could leave you in a serious lurch.
The COVID-19 crisis has also made things real for many businesses. Governments required organizations across industries, regardless of size, to migrate to remote work. Companies with business continuity plans in place responded with greater agility, whereas others were left scrambling.
Now, many countries are beginning to slowly reopen for business. Sure, there are constraints, but the idea is to get the global economy up and running. While you’re adapting, take some time to revise your business continuity plan.
It’s better to get your decision-makers around a table (or in a virtual meeting) now, while things are calmer. Most people think more clearly when not in the midst of a crisis. So, be proactive. Plan now for the worst. You can weigh up options at leisure, pursuing many different what-ifs to determine the best plan of attack.
Look back at what worked and what didn’t during the COVID-19-related disruptions. This review can provide real insight into opportunities, and you’ll be even better prepared in the future.
Planning with an MSP Partner
Business continuity plans lay out how the business will move forward amidst disruption. Work with a managed services provider (MSP) to ensure your planning is comprehensive. Our IT experts can help enable remote work, set up data protection, and develop a backup setup.
Send us a message at help@prodigyteks.com. Put a business continuity plan in place, and be more confident you’re ready for whatever happens next.

Your business has the OK to go ahead and get back to work on-site. You want to return to your office, but you don’t want to risk people’s health by doing so. After all, some say it’s too soon to go back. Plus, others predict a second wave of COVID-19 is likely. These suggestions can help you return to work while prioritizing safety.
Not everyone will welcome the call back to the corporate environment. Some employees may still be in a population vulnerable to the virus. They may want to take leave instead of returning to the work environment. Others may simply not show up.
Have your HR team send out a written notice informing employees of the timeline for returning to the office. Educate them about precautions you’re taking to provide a safe work environment. Ask for a written response of people’s intentions. Then, IT can start establishing procedures for getting everyone back to work.
You may have had great success with remote working during the quarantine. This could position you to allow workers to stay home if they are at risk or oppose the idea of returning “too soon.”
For those coming back, support social distancing by phasing in people’s return. Your business could also use a hybrid IT solution to allow people to come in just three days a week, and they could continue to work two days at home. This allows staggered re-entry and reduces the number of people on-site at the same time.
Back-to-Work Technology
You may be thinking you already have all the tech you need to go back to the office. C’mon, you were already working from there before this whole thing started. Plus, now you have all the new tools you added to support remote-employee productivity.
Still, you may not have invested in a long-term remote-work solution that will now support a hybrid model. Or perhaps the on-site tech you’ve long relied on isn’t meant to handle remote working for the long haul.
To achieve a flexible hybrid model, go with cloud solutions, or expand on-site IT. Do you need to add infrastructure to handle remote employees using virtual private networks (VPNs)? Both on-site staff and off-site workers might need to securely access systems at the same time.
Adopting cloud collaboration software allows co-workers to access network resources simultaneously, regardless of location. Or with virtual desktops, employees can access the same files and business applications on their work machines or on a personal device.
Bringing people back to the office, you’ll want to rethink the physical setup. Support social distancing by spreading employees’ seating arrangements out more. This will require moving around computer hardware, too.
If you were previously sharing technology, you’ll also need to add more desktops. Or you might invest instead in more laptops or portable devices. This could mean securing more software, too.
Added IT Precautions
Finally, cybercriminals are opportunistic. They’re already exploiting people with malware promising vaccines or cheap masks. These bad actors are also looking to exploit the tech demands on businesses. Many businesses adapted to a new way of doing things: they moved files to the cloud, and they allowed employee access from personal devices, but they did so quickly.
Explore any new vulnerabilities from your transitions. This is a good time to double-check permissions. Ensure that accountant Jane can access staff wage data but that receptionist Jenny can’t. Also, confirm that all virus protection and security patches are current.
Active planning is the answer to a smooth return to work. While offering protective coverings and ramping up cleaning in the office is important, make sure that you don’t overlook your technology needs.
Our IT experts can help you adapt nimbly. Contact us today at 312-600-8357 or info@prodigyteks.com!

Working from home is a big change in an already tumultuous time. Yet there’s a bright side. The quarantine could be your opportunity to reinvent how you work — for the better. Migrating to Microsoft Office 365 has benefits now. Plus, when you’re back to business as usual.
Office 365 is the cloud-based version of Microsoft Office. With a subscription, you get both the desktop and online versions of apps you already know. This includes Outlook, Word, Excel, PowerPoint, OneNote, SharePoint, Teams, Yammer, and more.
Office 365 enables collaboration in many ways, on desktops, tablets, and smartphones. For example:
Remote Work with Teams
Microsoft teams at its core is a chat program. But it does so much more. On all your devices, both iOS and Android, Teams allows “channels”. You can have company-wide or small task group channels. Or use a separate channel to instant messaging to a single person.
You can also invite clients or customers into channels to join the discussion. Additionally, you can set up security features that filter what they can access. You don’t want them to know the ingredients to your secret sauce!
Within Teams channels, users can share documents, spreadsheets, and presentations. Teams also integrates with other software. The options include Zendesk customer support, Asana project management, or Zoom video conferencing.
Using Teams in Office 365 creates a streamlined platform for remote work.
Remote Work with OneDrive
Working in the office, your users always had access to the business file server. OneDrive is the cloud equivalent. Yet, since it’s online, it’s always accessible. Microsoft’s hosts the file storage to let you access and share work files from all your devices.
Employees can even work offline. Any changes or edits to files automatically upload when you next connect.
Share OneDrive folders or files with external partners as well. Again, you can secure access with limits on who can see what and specifying what actions they can take. You can even set up automatic revoke access after a set time limit.
Office 365 & Business Security
An Office 365 subscription protects from viruses and cybercrime. It also offers ways to recover your files from malicious attacks.
Office 365 apps update with security patches without any effort on your part. Plus, Outlook scans email attachments and checks links for viruses or phishing scams.
OneDrive helps you restore files, so they’re not held captive in a ransomware attack. Office 365 also lets users encrypt email, prevent forwarding, and secure sensitive files.
Office 365 lets your business communicate and collaborate in real-time. Work on any device, anywhere, at any time. Enjoy business agility and flexibility with internal and external users.
Migrating to the cloud isn’t as simple as pressing the “start” button. Still, our tech experts can get you up and running quickly and with ease. Let us help you go online and get back to business as usual, even working remotely. Call us today 312-600-8357.
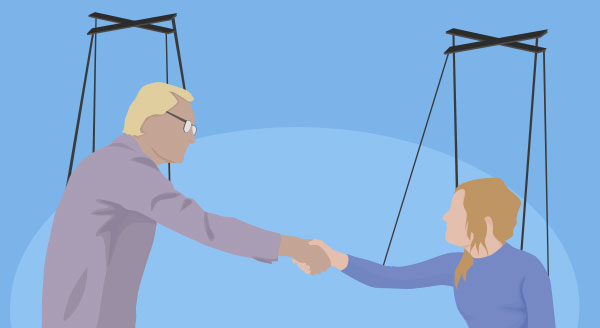
You can have top-notch security in place but there is still one danger: social engineering. It’s the old kid on the block, but most of us have never heard of it. Perhaps the more familiar term is ‘con’: the art of manipulating people to take certain actions or divulge private information. Social engineers are a special type of hacker who skip the hassle of writing code and go straight for the weakest link in your security defenses – your employees. A phone call, a cheap disguise or casual email may be all it takes to gain access, despite having solid tech protections in place.
Here are just a few examples of how social engineers work:
Email: Pretending to be a co-worker or customer who ‘just quickly’ needs a certain piece of information. It could be a shipping address, login, contact or personal detail that they pretend they already know, but simply don’t have in front of them. The email may even tell you where to get the data from. The hacker may also create a sense of urgency or indicate fear that they’ll get in trouble without this information. Your employee is naturally inclined to help and quickly sends a reply.
Phone: Posing as IT support, government official or customer, the hacker quickly manipulates your employee into changing a password or giving out information. These attacks are harder to identify and the hacker can be very persuasive, even using background sound effects like a crying baby or call-center noise to trigger empathy or trust.
In-person: A delivery man uniform gets past most people without question, as does a repairman. The social engineer can quickly then move into sensitive areas of your business. Once inside, they essentially become invisible, free to install network listening devices, read a Post-it note with a password on it, or tamper with your business in other ways.
It’s impossible to predict when and where (or how) a social engineer will strike. The above attacks aren’t particularly sophisticated, but they are extremely effective. Your staff has been trained to be helpful, but this can also be a weakness. So what can you do to protect your business? First, recognize that not all of your employees have the same level of interaction with people, the front desk clerk taking calls all day would be at higher risk than the factory worker, for example. We recommend cyber-security training for each level of risk identified, focusing on responding to the types of scenarios they might find themselves in. Social engineering is too dangerous to take lightly, and far too common for comfort.
Talk to us about your cybersecurity options today. Call us at 312-600-8357
