With the world grappling with a health pandemic, scams are shocking. Regrettably, bad actors are everywhere, always looking for opportunities, and they’re seeing one in the coronavirus. This article outlines what you need to watch out for and how to stay cyber safe.
The last thing you want to read right now is that there’s another threat out there – sorry, but it’s true. Cybercriminals take advantage of fear. They take timely concerns and use them to target victims. Using the anxiety and upheaval around coronavirus is their mission.
So far, several coronavirus-related attempts to cyberscam people have been reported. There are examples of:
- emails that appear to come from government health departments;
- offering a tax refund to get people to click on malicious links;
- memos to staff that appear to come from large employers;
- COVID-19 test offerings from private companies;
- fake websites promising to sell face masks or hand sanitizer;
- soliciting donations to help fund a vaccine.
What to Watch Out For
Another concern is the number of bogus websites registered with names relating to COVID-19. The site can look legit but is set up to steal information or infect the victim’s computer with malware.
You may get an email promising the attached information offers coronavirus safety measures, or information shared by the World Health Organization (WHO) if you click on the link, or a similar email pretending to be from a reputable news source, such as the Wall Street Journal (WSJ).
In another example, an email impersonating a healthcare company’s IT team asked people to register for a seminar “about this deadly virus.” Anyone who didn’t question why IT was organizing the meeting clicked to register. By filling out the form, they gave their details to hackers.
What to Do
Be cautious. It’s understandable that you’re anxious, but don’t let that stop you from taking cyber precautions. You should still:
- be wary of anything that tries to play on your emotions and urges immediate action;
- question where emails are coming from – remain vigilant even if the communication appears to come from a reliable source;
- hover over links before clicking them to see where they will take you – for example, in the WSJ example, the Web address was for the “worldstreetjournal”;
- avoid downloading anything you didn’t ask for;
- doubt any deals that sound too good to be true (“a mask that stops the virus 99.7% of the time!”);
- ignore any communications requesting your personal information;
- don’t be suckered by fraudulent pleas for charity.
Global health organizations generally do not send out emails with advice. Instead, navigate directly to that reputable health institution for real news.
If you’re still not sure about the validity of the communication, check it out. Do so by calling or using another medium to get in touch with the “source” of the received message.
While there is not yet a vaccine for COVID-19, you can put anti-virus protection on your computer. Also, make sure that you’ve applied all available security updates to keep your software safe.
We hope you’ll take care and stay healthy both physically and online in these tough times.
Need help installing security software and keeping your technology safe? Our cybersecurity experts can give your home a tech immunization. Contact us today at 312-600-8357!


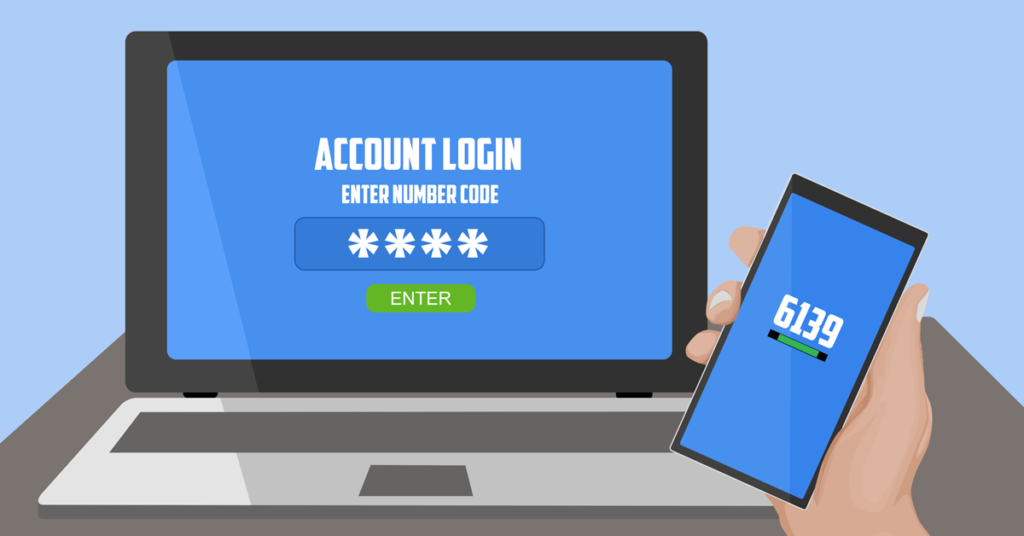





 The Internet has become a must-have in every household. However, the Internet presents its fair share of challenges especially when it comes to cyber-attacks. Hackers can steal your information such as credit card numbers, passwords, tax information or even disable your device. The following tips will help you browse safely and avoid such problems when online.
The Internet has become a must-have in every household. However, the Internet presents its fair share of challenges especially when it comes to cyber-attacks. Hackers can steal your information such as credit card numbers, passwords, tax information or even disable your device. The following tips will help you browse safely and avoid such problems when online.
