
No matter what type of business you have – law firm, manufacturing facility, or dentist office – phishing is one of the big threats to your data and technology infrastructure.
Falling prey to just one phishing email can cost a small business as much as $100,000. Losses come from a variety of areas, including lost productivity, cost of emergency remediation, lost business, and more.
88% of companies reported seeing spear phishing attacks in 2019.
Phishing emails are the main delivery method for ransomware, viruses, and other forms of malware. Phishing is also responsible for a majority of data breaches and compromised login credentials.
Knowing how to avoid common phishing tactics is a vital part of any Chicago business’ cybersecurity solutions. This includes ensuring that employees are aware of the ploys to watch out for and how to spot them in their inbox.
Unfortunately, phishing scammers have been taking advantage of the pandemic and the resulting change in normal routines, potential confusion about office policies, and desire for COVID-19 information. According to the U.N. Security Council, in just the first quarter of this year, there was a rise in phishing websites of 350%.
Have your employees been trained on phishing awareness recently? Read on for several tactics they need to avoid.
How to Identify Tactics That Phishing Scammers Use to Trick You
Sending an Email from a Domain You know
One dangerous phishing tactic that scammers use is to spoof an email address with a domain that you know. It may be an email from your own company or one from a company you have a relationship with, such as your web hosting service or bank.
This can be done in two ways:
- Using code to put another address in the “From” line that isn’t the address that sent the message at all.
- Compromising a user account and using that account to send out phishing emails.
If a user looks up and sees an email address they recognize in the “From” line of an email, they’re much more likely to trust the message and take the action requested, which may be to open an attachment or click a link.
Avoid falling for this by always following up with the purported sender if an unexpected email is received. Especially one that has a file attachment or link included.
You can also view the source code of the message in your email application to see if the true sending path matches the email address in the “From” line.
Spoofing The Look of a Well-Known Company
One of the common phishing tactics used is to send a fake order receipt or an urgent email asking to reset an account password. These often fool recipients because they may look identical to a real email from that same company.
For example, the phishing fake will use the company’s logo, verbiage from a real email, and even the standard signature.
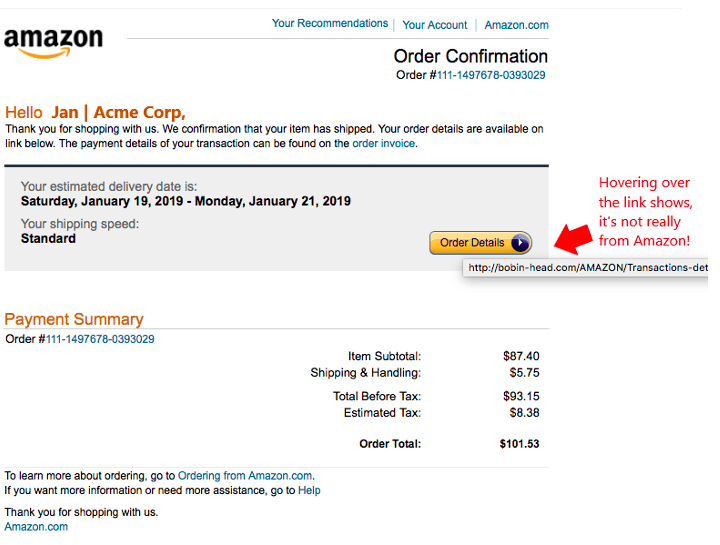
One of the quickest ways to reveal a fake is to hover over any links that are in the email without clicking on them. This will show in a popup the real URL of the link.
Emotional Tactics
Ever since the old “Nigerian Prince” scams of the early 2000s, phishing attackers have been using emotional tactics to get people to take the desired action on an email.
Some of the key emotions they will try to trigger include:
- Fear
- Urgency
- Curiosity
- Anger
- Excitement
When people feel an emotional response to a message, they will often click a link or open an attachment without thinking and unleash malware on their network.
Tactics include using words like “Immediately” or threats of what may happen if you don’t take action, like “You’ll lose account access.”
Fake order emails can elicit anger from someone who thinks an order mistake was made and is costing them money.
Employees should be very suspicious of any unexpected email in their inbox, but especially so if it is designed to elicit an emotional response to act without thinking.
Personalization
If you get an email that says, “Dear Sue” instead of “Dear Recipient,” you may be more inclined to believe it’s real because it’s personalized. How else would someone know your name, right?
In a world where large lists of users are sold on the Dark Web and the ease of finding nearly anyone on sites like LinkedIn and Facebook, personalizing your email is easy for hackers.
Personalizing phishing emails is a common tactic used by scammers and is designed to gain your trust.
Be aware that your name, company name, and even your title at the company may be easily found online, and just because they’re used in an email message, doesn’t make the message any less suspicious.
Get Help Building Strong Phishing Protections
ProdigyTeks can help your Chicago area business put systems in place that help prevent breaches due to phishing attacks. These include things like web filtering, email filtering, and more.
Schedule a free phone consultation today! Call 312-600-8357 or reach us online.



Leave a Reply